Home › Forums › Computers, Games and Technology › Web privacy
This topic contains 16 replies, has 10 voices, and was last updated by ![]() Rennie 3 years, 10 months ago.
Rennie 3 years, 10 months ago.
- AuthorPosts
A request for opinions from my more knowledgeable MGTOW brothers.
I use to be a regular at another forum. It used to be a place where opinions could be expressed openly but now has the warning “Don’t bother trying to use proxies because we can back track them…we’ll pass your details on if the old bill come knocking.” ( “old bill” are police )
My question; can you be back tracked through a proxy server? How about a VPN, how about TOR?
I’m currently using TOR for most of me web needs, it’s a bit slow but I’m willing to accept that to keep Big Brother and the thought police in their place. I also signed up for a free Tutanota e-mail account with end to end encryption between other account holders. I’d definitely recommend Tutanota.
“Long is the way and hard, that out of Hell leads up to light.”
If one man can invent a way to disguise his tracks, then another man can devise a way to undo his labors and track him.
For example, the US Govt broke into Tor years ago. Yes, Tor will keep out casual snoopers, but it will not keep out someone who is willing to invest the time and energy necessary to track you down.
For another example, government agencies are buying old fashioned manual typewriters — electrics will not do — for the purpose of getting around hackers. If governments have to do this, then draw the obvious conclusion about your own privacy.
Society asks MGTOWs: Why are you not making more tax-slaves?
If governments have to do this, then draw the obvious conclusion about your own privacy.
That being said, a VPN is good for masking yourself from SJW groups and corporations. Those that will take your ISP address and backtrack you.
We are small fries to governments. The whole point of MGTOW is to go below the radar and not cause problems.
I’ll give some context, as this is within my professional field. When someone says something’s “secure”, what they really mean is:
“It’s secure ***up to a point***. My Captain Crunch decoder ring is ‘secure’ against a 5 year old. But not against a college kid with a knowledge of basic statistics. My credit card that i use to buy stuff from Amazon.com is secure from the college kid, but not from the National Security Agency.”
In general, the capability of malicious agents is as follows, from least to most skilled:
– 5-year old
– Talented high school kid
– Individual specialists (think the “brilliant” system admin-type)
– Organized/semi-organized nonprofits (al Qaeda/Hacktivists)
– Organized crime/profit motive (think Mafia/Eastern Bloc, not local drug gangs)
– Governments – Law enforcement (FBI, DEA, RCMP)
– Governments – intelligence agencies/military (NSA, MI*)So for your SJW concerns, unless they’re backed up by Anonymous, they’re going to have limited capabilities. An offshore proxy** or VPN should be fine.
On the other hand, if you’re looking to set up a international drug market, a la SilkRoad, you’re going to have the FBI after you. TOR is a *minimum* requirement in that case, and recall the SilkRoad guy was busted.
Does that all make sense? I’m still working on my morning coffee.
**Caveat: Anyone can set up a proxy. If i fool you in to using my proxy, i can read a lot of what you’re doing. Make sure the proxy service you’re using is well-regarded, not a ‘fly by night’ operation.
What Faust for Science said.
As a group, MGTOW has no interest in political change or engaging in criminal activities so Government agancies will have little interest in us unless feminist manage to get some stupid crazy law enacted because something hurts their feelings.
It could happen, but when you get right down to the Brass tacks of what MGTOW is, it’s just a group of men who prefer to remain Batchelors instead of settling down into a long-term relationship or marriage.
Most of us are hard working, law abiding citizens with careers.
For example, the US Govt broke into Tor years ago
@roydal do you have any links on this? Do you remember if it was intelligence agencies or law enforcement?
Anonymous0“Web privacy”?? No such thing.
@RoyDal do you have any links on this? Do you remember if it was intelligence agencies or law enforcement
Apparently neither, the government paid a university ( CMU ) to do their dirty work for them. That was back in 2014 so I guess the folks behind Tor have learned by their mistakes and now have a more secure network.
https://motherboard.vice.com/read/cmu-sei-software-engineering-institute-dod-funding
I think they did it by infiltrating Tor to provide false nodes. If “the man” can control the 1st and 3rd node in a tor circuit then they can identify the source IP address. A simple way to fight this type of attack is to add extra nodes to the tor circuit.
“Long is the way and hard, that out of Hell leads up to light.”
Most of us are hard working, law abiding citizens with careers.
And good people.
The only reliable identifier for our members is an email. We don’t even ask for anything else except a country / city so your bros can know where others might come from, or if they read your posts (and it’s not perfect English) they can say “Oh! Well he’s from Poland!
The entire idea that MGTOW need to concern themselves with being overly cautious has been practically obliterated.
When a feminist releases a video that says “men belong in concentration camps” and we discuss it here, someone’s going have REALLY HARD TIME making MGTOW out to be the bad guys.
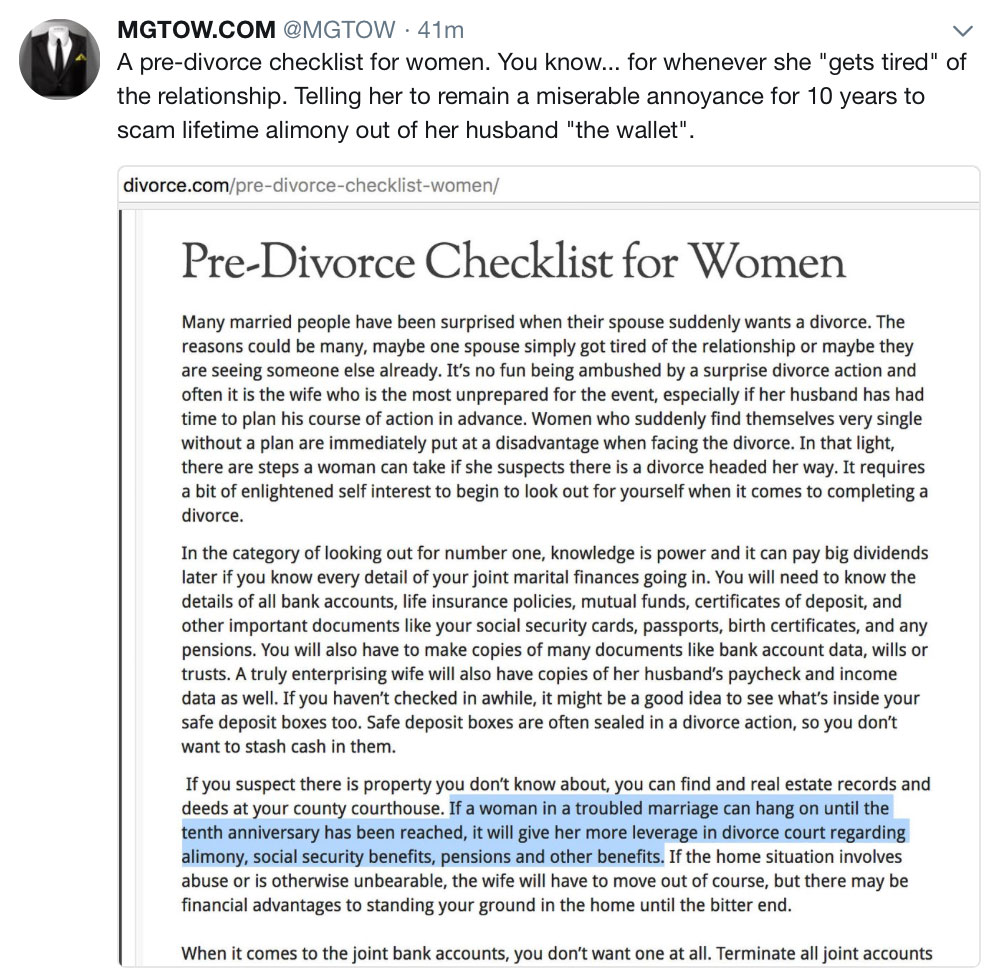
Even just yesterday on twitter. A s~~~storm of “TakeDownMRA” feminists tried to demonize / mock MGTOW with a tweet “Who would ever admit to their colleagues that they are MGTOW??” while showing a picture of a MGHOW crashing a slutwalk.
….to which you can point and laugh and ask them “how is that any worse than openly advertising yourself as a proud slut?” The MGHOW is the only one there with any class.
They got pretty quiet pretty fast.
If you keep doing what you've always done... you're gonna keep getting what you always got.What Faust for Science said.
As a group, MGTOW has no interest in political change or engaging in criminal activities so Government agancies will have little interest in us unless feminist manage to get some stupid crazy law enacted because something hurts their feelings.
It could happen, but when you get right down to the Brass tacks of what MGTOW is, it’s just a group of men who prefer to remain Batchelors instead of settling down into a long-term relationship or marriage.
Most of us are hard working, law abiding citizens with careers.
I think you’re overstating the charter. As a group mgtow basically believe that relationships with women should be evaluated rationally. Acceptance of the political status quo, through apathy, is just your personal non mgtow related belief. But we do allow personal political discussions here. Cuz it’s fun.
From my understanding, MGTOW isn’t advocating for political change or at least not from my understanding of it. We often talk about how f~~~ed up the system is with regards to gender politics, but i don’t see anyone being politically active in trying to change that.
I’ve walked away from the table. Call that apathy if you will, but i’m happy with my life as it is. I’ve no desire to go down the MRA route.
(…)I’m currently using TOR(…)
That’s about as good as you can hope really, I’m guessing you’re asking this because of things like that Canadian guy facing jail time for disagreeing with a feminist?
Like MattNYC said, it’s levels of security, TOR will discourage people for persecuting free speech well enough, I don’t see the law enforcement going after you, even if you say “kill all women.”(…)the US Govt broke into Tor years ago(…)
I’m not sure what you mean here, it was the US Navy that created TOR in the first place, and the idea for it was specifically to keep the information private and anonymous, so US agents across the world could communicate without being eves dropped, TOR only made it to the general public because the US Navy made it so, since the more nodes it has, the more secure the connections are, but they can’t control it at all.
Look for a paper the NSA wrote titled “TOR Stinks” in it they discuss possible ways to control the TOR network, but it’s pretty futile really since the system was specifically thought up to avoid monitoring.(…)if you’re looking to set up a international drug market, a la SilkRoad, you’re going to have the FBI after you. TOR is a *minimum* requirement in that case, and recall the SilkRoad guy was busted(…)
That’s not that simple, it took 3 years and around 100 agents from both the FBI and CIA (rumour, take it with a grain of salt) to get to Ross William Ulbricht, which was allegedly the guy behind “Dread Pirate Roberts” the administrator of the SilkRoad, and I say allegedly because the case was flimsy at best, Ulbricht only got a conviction because he admitted he created the SilkRoad, although he denied he was the one running it and was just the fall guy.
But since we’re talking about this I’d like to warn everyone that uses BitCoin, I’ve always warned people not to use it, and if nothing else look at the value of BitCoin back when the FBI was seizing the BitCoins of Ulbricht, it took a massive nose dive, if you think your money is safe in there, it’s not, in some countries it’s technically illegal to have/use BitCoins.
The only reason we don’t see more cases like the one in China where they tried to ban BitCoin, is because it would take a lot of effort to do so, and also you can bet some corrupt government officials have money in there.
But just as buying anything with gold is illegal in almost every country in the world, the same laws apply to BitCoin, since it’s a parallel unregulated currency, in court anyone with BitCoins could get nailed by the right judge/persecutor.mistermansmithmgtow.blogspot.com
Unless you are into some absolutely crazy stuff like, online drug markets/ Pedo stuff, using TOR is 100% safe. TOR traffic can be sniffed though, so even while using TOR, don’t post info that can identify you.
An ISP address alone is not enough to identify you specifically, but probably where you live to within a few km. Regardless it’s still a good idea to get in the habit of obfuscating as much as possible.
I would stay away from proxy servers. Not only are they abused to hell by spammers, but you have no idea if they are keeping any logs. The cops will probably go after the proxy server if it’s used to do illegal stuff. They are often also slow because of overuse and probably lack the ability to deal with DNS leaks.
Tor is pretty solid. But you need to use the browser version unless you know how to properly use TOR itself. Global scripting should be disabled on it and you have to watch out for compromised sites. Basically don’t do anything too illegal with it and don’t do it often if you do.
A VPN subscription to a reputable provider is your best bet. DO NOT use any “free” VPN’s like VPNbook. Make sure they don’t keep logs, read the reviews of the service by third parties often. Torrentfreak has a yearly review of VPN services. Make sure you cover your bases like kill switches(tunnel goes down all traffic stops) and DNS leak protection.
With TOR and VPN, even if they do try and backtrace you, they’ll get as far as the exit server and that’s it.
An ISP address alone is not enough to identify you specifically, but probably where you live to within a few km. Regardless it’s still a good idea to get in the habit of obfuscating as much as possible.
I would stay away from proxy servers. Not only are they abused to hell by spammers, but you have no idea if they are keeping any logs. The cops will probably go after the proxy server if it’s used to do illegal stuff. They are often also slow because of overuse and probably lack the ability to deal with DNS leaks.
Tor is pretty solid. But you need to use the browser version unless you know how to properly use TOR itself. Global scripting should be disabled on it and you have to watch out for compromised sites. Basically don’t do anything too illegal with it and don’t do it often if you do.
A VPN subscription to a reputable provider is your best bet. DO NOT use any “free” VPN’s like VPNbook. Make sure they don’t keep logs, read the reviews of the service by third parties often. Torrentfreak has a yearly review of VPN services. Make sure you cover your bases like kill switches(tunnel goes down all traffic stops) and DNS leak protection.
With TOR and VPN, even if they do try and backtrace you, they’ll get as far as the exit server and that’s it.
I agree with most of the above post but i’d like to disagree on some issues here.
1) An IP address is enough to identify a person specifically if the ISP uses static ip’s. My ISP uses static ip’s and anything i do can be linked back to me unless i use a VPN/Proxy/TOR
2) A VPN subscription with a reputable provider isn’t a person’s best bet but TOR is. Trusting TOR is a lot better than trusting a VPN provider.
An ISP address alone is not enough to identify you specifically, but probably where you live to within a few km. Regardless it’s still a good idea to get in the habit of obfuscating as much as possible.
I would stay away from proxy servers. Not only are they abused to hell by spammers, but you have no idea if they are keeping any logs. The cops will probably go after the proxy server if it’s used to do illegal stuff. They are often also slow because of overuse and probably lack the ability to deal with DNS leaks.
Tor is pretty solid. But you need to use the browser version unless you know how to properly use TOR itself. Global scripting should be disabled on it and you have to watch out for compromised sites. Basically don’t do anything too illegal with it and don’t do it often if you do.
A VPN subscription to a reputable provider is your best bet. DO NOT use any “free” VPN’s like VPNbook. Make sure they don’t keep logs, read the reviews of the service by third parties often. Torrentfreak has a yearly review of VPN services. Make sure you cover your bases like kill switches(tunnel goes down all traffic stops) and DNS leak protection.
With TOR and VPN, even if they do try and backtrace you, they’ll get as far as the exit server and that’s it.
I agree with most of the above post but i’d like to disagree on some issues here.
1) An IP address is enough to identify a person specifically if the ISP uses static ip’s. My ISP uses static ip’s and anything i do can be linked back to me unless i use a VPN/Proxy/TOR
2) A VPN subscription with a reputable provider isn’t a person’s best bet but TOR is. Trusting TOR is a lot better than trusting a VPN provider.
In the case of static IP’s, yes. But most ISP’s use DHCP. A static IP is usually a luxury and they either want extra money, or you to have a business account to have one. Why is that you ask? because the only reason someone would need a static IP is because they are running a server which is not usually allowed on residential accounts. I would dump any ISP using statics to try and hold it’s users accountable.
In the case of static IP’s, yes. But most ISP’s use DHCP. A static IP is usually a luxury and they either want extra money, or you to have a business account to have one. Why is that you ask? because the only reason someone would need a static IP is because they are running a server which is not usually allowed on residential accounts. I would dump any ISP using statics to try and hold it’s users accountable.
From where i come from, ISP’s do assign static ip’s for residential plans that come with unlimited usage. Obviously, things are different in your place.
I don’t have the luxury of dumping my ISP since there’s no other alternative.
In the case of static IP’s, yes. But most ISP’s use DHCP. A static IP is usually a luxury and they either want extra money, or you to have a business account to have one. Why is that you ask? because the only reason someone would need a static IP is because they are running a server which is not usually allowed on residential accounts. I would dump any ISP using statics to try and hold it’s users accountable.
From where i come from, ISP’s do assign static ip’s for residential plans that come with unlimited usage. Obviously, things are different in your place.
I don’t have the luxury of dumping my ISP since there’s no other alternative.
Still with the static IP, someone would have to be able to get at your ISP’s records to determine who was behind it, unless they already knew. Any ISP with a lick of sense will not just hand that information over to anyone.
Easy enough to solve the accountability problem. Just don’t use the external IP for anything dodgy. Just a get a VPN, or TOR, or A VPN with TOR running on top of it.
- AuthorPosts
You must be logged in to reply to this topic.
921526
921524
919244
916783
915526
915524
915354
915129
914037
909862
908811
908810
908500
908465
908464
908300
907963
907895
907477
902002
901301
901106
901105
901104
901024
901017
900393
900392
900391
900390
899038
898980
896844
896798
896797
895983
895850
895848
893740
893036
891671
891670
891336
891017
890865
889894
889741
889058
888157
887960
887768
886321
886306
885519
884948
883951
881340
881339
880491
878671
878351
877678